
Triple hammer time for video memory
GDDRHammer, GeForge, and GPUBreach: three new research papers diving into attacks that exploit the Rowhammer technique.

GDDRHammer, GeForge, and GPUBreach: three new research papers diving into attacks that exploit the Rowhammer technique.

Smart sex toys and their companion apps collect and process some extremely personal data. We break down the risks involved, and ways to protect your privacy.

How the AirSnitch vulnerability family threatens corporate networks, and what changes you need to make to your network architecture and settings to stay protected.

Kaspersky experts have detected fake websites that steal money from BTS fans during ticket pre sales. We explain how to stay vigilant and not fall victim to the scammers.

Protecting a security console is more critical than one might think. Here’s the lowdown on control-layer compromise, and how to keep it from happening.
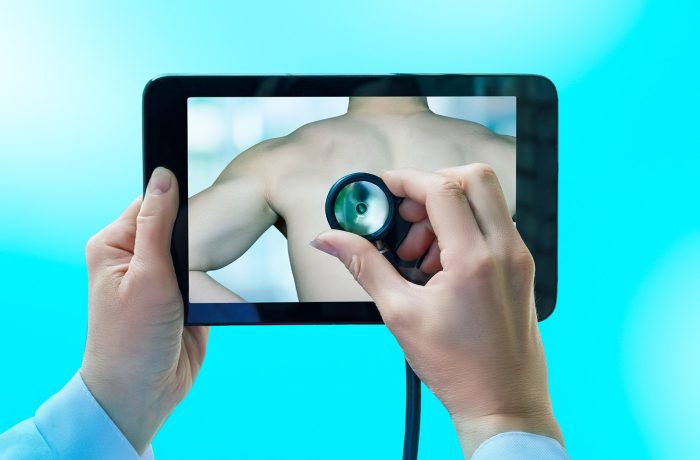
Telehealth services and apps are blowing up in popularity right now, making the availability of medical services better than ever. But just how safe is telemedicine, and what kind of risks does it carry?

How to manage vulnerabilities when developing or using open-source software.

How the AI boom and increasing reliance on open-source components are piling up corporate security debt — and what you can actually do about it.

The new CrystalX remote access Trojan looks like the prank viruses of the 90s on the surface, but it causes a lot more damage. It spies on all that’s happening on your computer, steals cryptocurrency and accounts, and gives the attacker full control over your device. We break down how it works, and how to avoid becoming a victim.
I firmly believe that the concept of cybersecurity will soon become obsolete, and cyberimmunity will take its place.
Eugene Kaspersky
We break down the BeatBanker trojan attack, which combines espionage, crypto theft, and mining with inventive ways to dig its heels into a smartphone.
Tired of hallucinations in AI overviews, and have no clue as to why or how Copilot suddenly appeared on your PC? Here’s a guide to switching off those intrusive AI features in popular services.
A browser-in-the-browser attack, theoretically described in 2022, has been adopted in real-world phishing. We break down how it works, and how to spot a fake authentication window.
An in-depth analysis of CVE-2026-3102, a vulnerability posing a potential threat to anyone processing images on a Mac.